Cloud data security is a set of measures and technologies designed to protect information that is stored and processed in a cloud environment. Cloud computing allows users to store, process, and access data via the internet using remote servers, which offers many benefits but also poses risks related to data security.
Cloud data security is crucial for several reasons:
Protection against data leaks:
Cloud data security is a set of measures and technologies designed to protect information that is stored and processed in a cloud environment. Cloud computing allows users to store, process, and access data via the internet using remote servers, which offers many benefits but also poses risks related to data security. Cloud data security is critical for several reasons:
Protection against data leaks:
– Data encryption: One of the key elements of data protection in the cloud is encryption. Data encryption ensures that data is converted into an unreadable form for unauthorized persons should it be compromised in any way. There are various forms of encryption, including disk-level encryption, data-in-transit encryption (e.g., using the HTTPS protocol), and application-level encryption.
– Access control: Managing access rights is another key aspect of data protection in the cloud. Organizations should have mechanisms to control who has access to specific data and what operations they can perform on it. This includes the use of identities and permissions, two-factor authentication, access policies, and other methods.
– Monitoring and auditing: An important element of data protection in the cloud is the monitoring and auditing of data flows and operations. Monitoring systems enable organizations to track who has access to data, how the data is being used, and whether any suspicious activity is occurring that could indicate a data breach.
Compliance with regulations and standards:
– Understanding and implementing regulations: An organization must have a clear understanding of the regulations and standards that apply to it in the area of data protection. For example, in Europe, an organization must comply with the GDPR, while in the U.S. healthcare sector, the HIPAA standard is important. Each of these regulations sets out specific data protection requirements that must be met.
– Implementation of appropriate measures: Based on the requirements of regulations and standards, organizations implement appropriate security measures to ensure that data is properly protected. This may include encryption, access control, conducting audits, and more.
Protection against cyber threats:
– Firewalls and antivirus software: Organizations often use firewalls and antivirus programs to protect their cloud environments from various types of cyber threats, such as malware, ransomware, and botnets.
– Security updates and patches: An important element is regularly updating and patching software and systems. This helps eliminate known security vulnerabilities that could be exploited by cyber attackers.
Employee security training: Most cyberattacks exploit the human factor. Therefore, it is important to provide employees with regular security training so they can recognize potential threats, such as phishing emails or social engineering.
Ensuring data integrity and availability:
– Data backup: To ensure data integrity and availability, it is important to perform regular data backups and have mechanisms in place to restore data when necessary.
– Data redundancy: Having redundant systems and backup mechanisms ensures that data remains available even in the event of a failure of one or more servers or devices.
User trust:
Transparency and communication: Organizations should communicate transparently with their users about the measures they take to protect data and provide them with information about security procedures and policies.
Credibility and reliability of cloud service providers: Users often rely on cloud service providers to ensure the security of their data. Therefore, it is important that cloud service providers adhere to strict security standards and provide transparent information about their security measures.
Data security in the cloud is a complex topic that requires an integrated approach and a combination of various security measures and technologies. Organizations should regularly review their security procedures and policies and update them in line with the latest threats and regulations.
Security in Cloud Environments
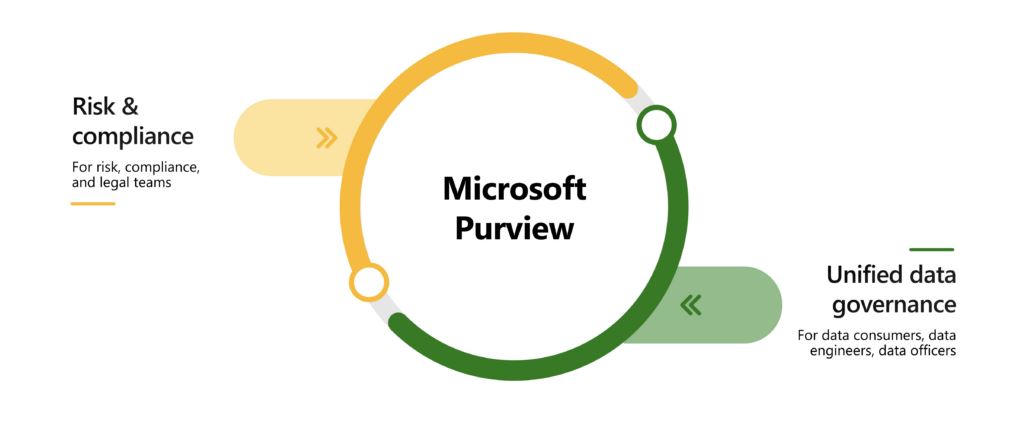
Azure is a cloud platform provided by Microsoft that offers a wide range of services for storing, processing, and analyzing data. One of the key services for securing and working with data in Azure is Office Purview.
Office Purview is a service provided within the Azure platform that is used to discover, classify, protect, and manage data across various sources and systems, including data in cloud and hybrid environments such as Office 365, SharePoint, OneDrive, Microsoft Teams, and others.
Below are some key elements and methods for securing data in the Azure environment, with a focus on Office Purview:
- Data classifications:
- Office Purview enables organizations to classify their data based on sensitivity, importance, or other criteria. Data classification enables a better understanding of data content and the application of appropriate security measures and access rules.
- Data protection:
- Office Purview provides tools for monitoring and managing data access. This includes tracking who has access to specific data and the ability to set rules and policies to control and restrict access.
- Sensitive data detection:
- With Office Purview, you can identify sensitive data, such as personal information, financial data, or confidential documents, and track its movement and usage within the organization.
- Automated metadata analysis and processing:
- Office Purview automatically analyzes and processes metadata from various data sources, enabling organizations to gain better visibility into their data and identify potential security risks.
- Integration with other data security and management tools:
- Office Purview is integrated with other services and tools within the Azure platform, such as Azure Active Directory for identity and access management, Azure Sentinel for monitoring and analyzing security events, and Azure Information Protection for data encryption and classification.
- Auditing and reporting:
- Office Purview enables organizations to audit data flows, track data-related events, and generate reports on data usage and compliance with regulations and standards.
Office Purview is thus a comprehensive service that provides organizations with the tools and functionality to manage, protect, and secure their data within the Azure environment and other cloud and hybrid environments they use. Integration with other services and tools in Azure enables organizations to create a comprehensive data security strategy that is both effective and holistic.
User trust:
Transparency and communication: Organizations should communicate transparently with their users about the measures they are taking to protect data and provide them with information about security procedures and policies.
Credibility and reliability of cloud service providers: Users often rely on cloud service providers to ensure the security of their data. Therefore, it is important for cloud service providers to adhere to strict security standards and provide transparent information about their security measures.
Data security in the cloud is a complex topic that requires an integrated approach and a combination of various security measures and technologies. Organizations should regularly review their security procedures and policies and update them in line with the latest threats and regulations.
Security in Cloud Environments
Azure is a cloud platform provided by Microsoft that offers a wide range of services for storing, processing, and analyzing data. One of the key services for securing and working with data in Azure is Office Purview.
Office Purview is a service provided within the Azure platform that is used to discover, classify, protect, and manage data across various sources and systems, including data in cloud and hybrid environments such as Office 365, SharePoint, OneDrive, Microsoft Teams, and others.
Below are some key elements and methods for securing data in the Azure environment, with a focus on Office Purview:
- Data classifications:
- Office Purview enables organizations to classify their data based on sensitivity, importance, or other criteria. Data classification enables a better understanding of data content and allows for the application of appropriate security measures and access rules.
- Data protection:
- Office Purview provides tools for monitoring and managing data access. This includes tracking who has access to specific data and the ability to set rules and policies to control and restrict access.
- Sensitive data detection:
- With Office Purview, you can identify sensitive data, such as personal information, financial data, or confidential documents, and track its movement and usage within the organization.
- Automated metadata analysis and processing:
- Office Purview automatically analyzes and processes metadata from various data sources, enabling organizations to gain better visibility into their data and identify potential security risks.
- Integration with other data security and management tools:
- Office Purview is integrated with other services and tools within the Azure platform, such as Azure Active Directory for identity and access management, Azure Sentinel for monitoring and analyzing security events, and Azure Information Protection for data encryption and classification.
- Auditing and reporting:
- Office Purview enables organizations to audit data flows, track data-related events, and generate reports on data usage and compliance with regulations and standards.
Office Purview is thus a comprehensive service that provides organizations with the tools and functionality to manage, protect, and secure their data within the Azure environment and other cloud and hybrid environments they use. Integration with other services and tools in Azure enables organizations to create a comprehensive data security strategy that is both effective and comprehensive.
You can find more technical articles, guides, and IT news on the website: www.virtualall.sk
