Industry 4.0, also known as the Fourth Industrial Revolution, which we have recently become a part of, is increasingly under threat, particularly due to cyberattacks. These attacks target industrial control systems, thereby threatening the entire operation of a business (product manufacturing or service provision). It is becoming increasingly important to focus on cybersecurity in the industrial sector as well.
Industry 4.0 is bringing about major changes in the industrial sector, and as its principles are implemented, it is transforming the very nature of industry as we have known it. The essence of this movement is to introduce and implement entirely new information technologies and to digitize processes, products, services, and equipment. The result of this comprehensive digitization should be the so-called Smart Factory, where people, machines, equipment, logistics systems, and products are able to communicate directly with one another and collaborate. Everyone will be connected to a single network where they can share all information with one another, thereby reducing the time needed for data transfer and decision-making. The implementation of such systems will streamline a company’s operations, reduce its costs, and conserve resources. However, along with all the positives comes a major risk: cyberattacks. These threaten not only information systems but also industrial control systems, upon which the manufacturing process and the digitalization of industry rely.
The most famous case is from Iran and illustrates very well how neglecting security within industrial control systems could cause a major problem not only for the organization but also for humanity. A computer worm known as STUXNET was used in this attack. It was a type of malware (i.e., malicious software) that managed to infiltrate the isolated network of an Iranian nuclear facility via an infected data storage device. This malware posed a truly significant risk, as it spread uncontrollably and even the systems were unable to detect it. It was able to disguise itself and thus “appeared” to be a normal part of the operating system. It managed to alter system settings, which led to physical damage and material losses. At the same time, it slowed down the Iranian nuclear program.
Another example of a cyberattack is the attack on a Ukrainian power plant back in 2015. Hackers managed to cripple the country’s power distribution network, leaving over 200,000 households completely without electricity.
There are more and more such cases, and they threaten the functioning not only of businesses but of the entire country. How prepared is Slovakia for such attacks?
The National Security Authority publishes a comprehensive annual report on the state of cybersecurity in Slovakia. The most recent figures pertain to 2022. Based on this data, Slovakia was primarily threatened by social engineering, which includes phishing attacks via SMS messages, emails, and phone calls. It was precisely in this area that a large number of phishing SMS messages purporting to be from Slovak Post occurred. The attacker’s goal was to trick the victim into opening a link contained in the message, which contained a virus. The message typically contained information regarding issues with package delivery. However, phishing attacks also occurred via email. Other types of cyberattacks in Slovakia included, in particular, DDoS attacks and the distribution of malicious code, i.e., malware. Attackers frequently sought to infiltrate systems and obtain the data they were interested in. Here, in many sectors, we encounter the problem of password policies. Often, passwords are not updated regularly, or the same password is used for years.
Based on audits conducted in various sectors, the National Security Authority (NBÚ) identifies the following problems in particular:
- an inadequate cybersecurity (CS) strategy,
- the cybersecurity manager is designated only as a formal role,
- serious deficiencies in the management of assets, threats, and risks,
- contracts with suppliers do not contain provisions regarding cybersecurity,
- lack of training in information security and data protection,
- operational logs are not maintained,
- there is no formally defined process for addressing and reporting security incidents,
- backup plans and backup requirements have not been developed,
- disaster recovery and business continuity plans are not tested.
The NSA report provides an individual overview of each sector and its cybersecurity status. If you are interested in more information regarding Slovakia’s results, you can find it here: Report on Cybersecurity in the Slovak Republic in 2022.
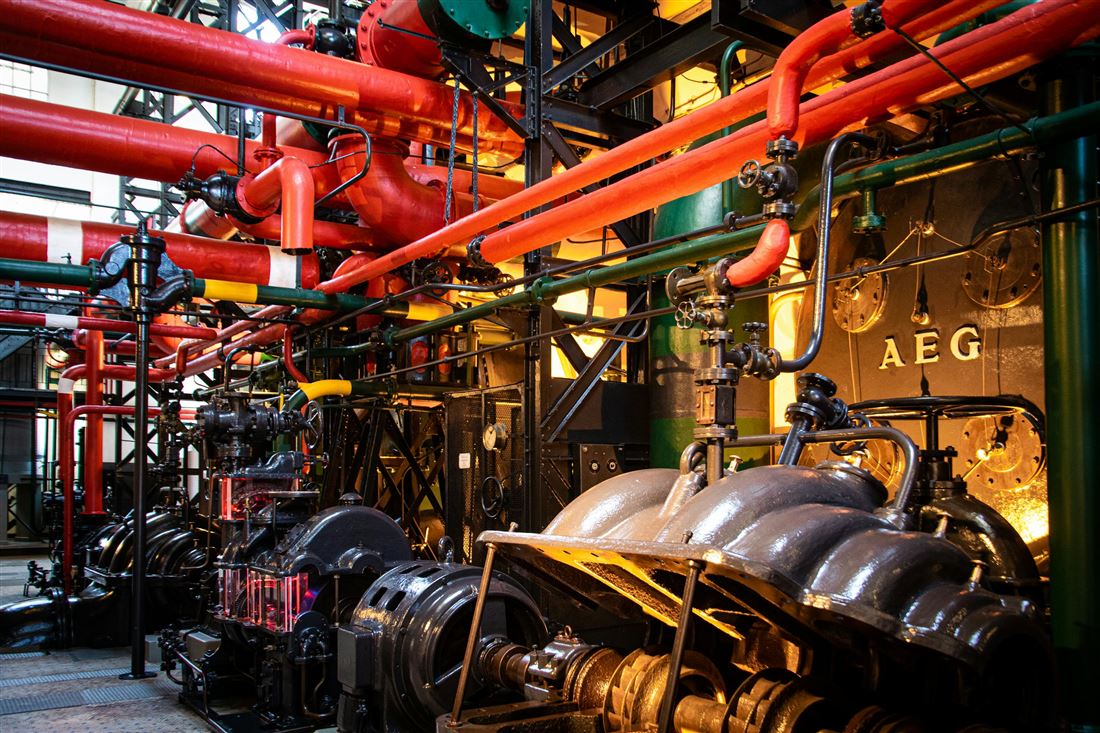
When we take a closer look at the industrial sector itself, the greatest weakness lies precisely in control systems, whose primary role is to manage production. The architecture and software in these systems are often very outdated and represent the greatest vulnerability. Until recently, these systems were only part of a very small internal network within the company. Today, however, they are connected to large networks and are accessible to a much larger number of people. In most cases, this fact is perceived as an advantage. Management has become more efficient, and access to information and control has accelerated; however, this has opened the door to cyber threats. Many of these industrial control systems (e.g., production lines) run on outdated operating systems and do not even use basic encryption. Since we do not view updating such systems as a necessity (since the line continues to produce without issues), they become a relatively easy target for hackers.
Cyberattacks are constantly evolving, and it is becoming increasingly difficult to defend against them. That is why we offer you several ways to prevent them.
UPDATES – systems must be kept up to date to prevent the exploitation of known vulnerabilities; at the same time, it is essential to update company policies, monitor trends, and adapt company processes accordingly.
TRAINING – It is essential to train employees in cybersecurity, including how to respond in the event of an attack, how to recognize a phishing email, and much more.
ACTIVE PROTECTION – It is important to have antivirus software that ensures system protection.
BACKUP – while backing up data will not prevent a cyberattack, it can minimize damage and ensure the smooth continuation of business processes.
PLANNING – every company should anticipate the possibility of a cyberattack and prepare accordingly, developing a plan and step-by-step procedures to follow in the event of a cyberattack.
CHANGE OF MINDSET – it is essential to realize that a cyberattack can affect anyone, and it is necessary to prepare for it by following rules (such as two-factor authentication, network segmentation, and others) that will help us avoid an attack.
Recent years have seen a major shift in technologies specifically designed for the industrial sector that can prevent cyberattacks. Of particular interest is the development of a system focused on detecting unauthorized access to the system, which could ensure seamless operation in the future despite the threat of attacks.
We strongly recommend being prepared for potential threats that could negatively impact the company’s operations. In other words, do not “rest on your laurels” under the assumption that because your production line is running and producing, there is no need to address its security. The current situation and forecasts highlight the risks associated with digitalization. It is important to prepare for them adequately, thereby mitigating the negative aspects and emphasizing the positive benefits that modern technologies can bring to industry.
SOURCES:
Report on Cybersecurity in the Slovak Republic in 2022
